Table of Contents >> Show >> Hide
- What the Study Really Tells Us
- Why Predictable Passwords Keep Winning
- The Real Risk: One Weak Password Becomes Many Problems
- What Good Password Security Actually Looks Like
- Why the Shift to Passkeys Matters
- The Workplace Lesson Hidden Inside Consumer Password Data
- Conclusion: Predictable Choices Are the Real Password Problem
- Real-World Experiences That Explain the Data
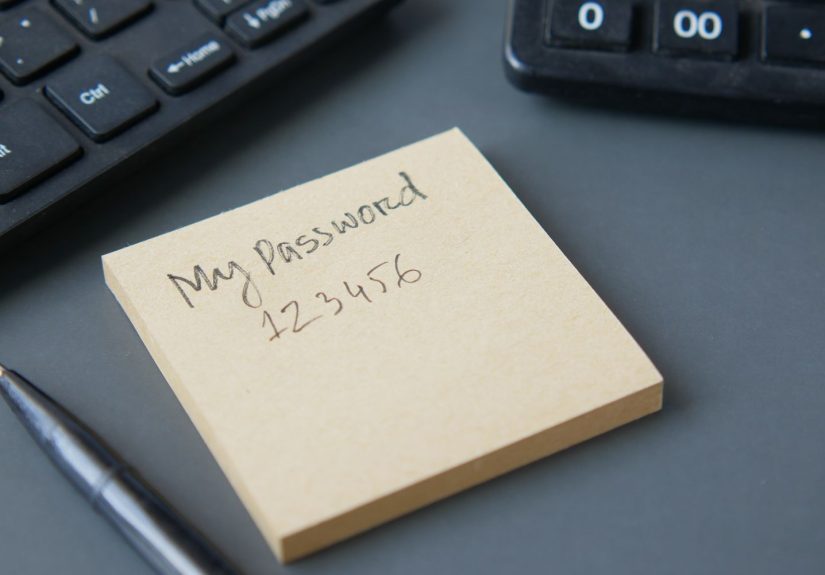
Americans have a complicated relationship with passwords. We know we should make them long, unique, and hard to crack. We also know that using “123456,” “password,” or anything involving a pet name, a birthday, or blind optimism is not exactly cybersecurity excellence. And yet, password studies keep finding the same thing: when left to our own devices, many of us still choose logins with all the unpredictability of ordering fries at a diner.
That is the central takeaway from recent U.S. password research. The details may shuffle around a little from year to year, but the pattern stays hilariously, alarmingly familiar. Americans continue to favor short, common, reusable, and deeply guessable passwords. The names change. The bad habits do not. One year it is “secret.” Another year it is “admin.” The evergreens like “123456,” “password,” and keyboard walks such as “qwerty123” never seem to miss the reunion.
On paper, this sounds like a minor digital misdemeanor. In practice, it is a major security problem. Predictable password choices are not just lazy. They are scalable. A weak password on one account can become a weak point across many accounts, especially when people reuse it. That turns one forgettable login into a skeleton key for email, banking, shopping, streaming, cloud storage, school portals, and work apps. In other words, the password you created while half-asleep can become tomorrow’s full-time crisis.
What the Study Really Tells Us
The headline is not merely that Americans choose weak passwords. It is that Americans choose weak passwords in very recognizable patterns. The most common choices usually fall into a few familiar buckets: simple number strings, obvious words, common keyboard patterns, sports terms, affectionate phrases, and slight variations designed to look clever without actually being secure.
That means the usual suspects keep showing up:
- Number chains like “123456,” “12345678,” and “123456789”
- Literal choices like “password” and “password1”
- Keyboard strolls like “qwerty” and “qwerty123”
- Easy dictionary words like “secret,” “princess,” and “sunshine”
- Cultural comfort-food passwords like “football,” “baseball,” and “iloveyou”
None of these are random. They are memorable, fast to type, and emotionally familiar. That is exactly why they are so common, and exactly why they are so weak. Humans like convenience. Attackers like convenience too. Unfortunately, those two interests overlap more than anyone should feel comfortable about.
The deeper lesson is not that people are uninformed. It is that people are overloaded. The average internet user now juggles a ridiculous number of accounts. A person may have one login for work chat, one for payroll, one for online banking, several for shopping, a few for streaming, at least one abandoned fitness app they forgot existed, and three websites that still email them promotional codes with the emotional urgency of a hostage negotiation. Under that kind of password sprawl, predictability starts to feel efficient.
Why Predictable Passwords Keep Winning
1. People remember stories better than entropy
A random 18-character password is strong. It is also about as lovable as a parking ticket. Most people gravitate toward passwords they can remember without effort, which often means names, dates, favorite teams, or reusable patterns. The human brain prefers meaning. Security prefers randomness. Guess which one usually wins during a rushed account setup at 11:47 p.m.?
2. Password fatigue is real
Modern life requires too many credentials. Once people hit account number twenty, they stop composing elegant security secrets and start improvising survival tactics. That is how one decent password becomes five recycled versions of itself. Add a capital letter here, a number there, maybe an exclamation point for dramatic flair, and suddenly the same basic password is doing a nationwide tour.
3. Many users mistake “different-looking” for “secure”
People often believe that changing “password” into “P@ssword1!” is a major upgrade. It is not. That is not a disguise. That is a fake mustache. Attackers and password-cracking tools have seen every version of this trick a million times. A password can look busy and still be easy to predict.
4. Convenience beats caution until something goes wrong
This may be the most human factor of all. A weak password rarely feels dangerous in the moment. It feels fast. The consequences are delayed, invisible, and easy to ignore. Until the login alert arrives. Until the password reset emails start landing. Until the streaming account, email inbox, or store wallet gets hijacked. Security often loses because the risk is abstract, while convenience is immediate.
The Real Risk: One Weak Password Becomes Many Problems
This is where the story stops being funny. Password predictability matters because account attacks are industrialized now. Attackers do not need to sit in a dark room guessing your dog’s name by candlelight. They use automation, leaked credential lists, phishing kits, and credential-stuffing tools that can test huge numbers of logins quickly and cheaply.
If you reuse a password across multiple services, a breach on one site can spill into others. A forgotten forum account from years ago can become the doorway into your current email, which then becomes the reset hub for half your online life. That is the magic trick no one asked for: one weak password turns into three compromised accounts before you have finished your coffee.
This is also why predictable passwords are a business issue, not just a personal one. Employees do not magically become cybersecurity monks during office hours. If a person tends to favor convenient passwords at home, that habit can follow them to workplace logins too. Studies on common passwords have repeatedly shown overlap between personal and corporate password behavior, which is unsettling for anyone who enjoys functioning systems, stable customer trust, or not explaining a breach to legal counsel.
And the business consequences can get expensive fast. Credentials remain one of the simplest ways into accounts and systems because they exploit the oldest vulnerability in security: people are busy, tired, and optimistic. Attackers count on that. Too often, they are right.
What Good Password Security Actually Looks Like
The good news is that the fix is less glamorous than people think, but more manageable too. You do not need to become a cryptography wizard. You need a system that reduces guessability and reduces reuse.
Use passphrases, not flimsy little passwords
Longer is better. A passphrase made of unrelated words is stronger and easier to remember than a short “clever” password. Something like “lamp-tulip-river-comet-window” beats “Tiger2024!” by a mile. One sounds absurd. That is a feature, not a bug.
The key is randomness. If the phrase feels like something you would naturally say, it is probably too predictable. Good passphrases should sound a little weird, like they were generated by a caffeinated poet.
Use a password manager
Password managers solve the core problem most people actually have: too many accounts, not enough brain space. They generate long, unique passwords for each site and store them securely, so you only need to remember one strong master passphrase. This does not remove all risk, but it dramatically improves your odds because it breaks the reuse cycle.
If you are still trying to remember every login manually, you are basically doing clerical work for your own anxiety.
Turn on multi-factor authentication
A password alone is no longer enough for important accounts. Multi-factor authentication adds a second barrier, which means an attacker who steals or guesses your password still has another hurdle to clear. It is one of the simplest and most effective upgrades available. No fireworks. Just better odds.
Move to passkeys when available
The industry is slowly, and with the emotional pace of a reluctant housecat, moving toward passwordless sign-in methods such as passkeys. These systems rely on device-based authentication and cryptographic methods rather than a traditional password you type. They are easier for users and harder for attackers to phish. That matters because the best password may eventually be the one you no longer have to invent.
Why the Shift to Passkeys Matters
The push toward passkeys is not some trendy Silicon Valley rebrand for common sense. It is a recognition that passwords ask too much of humans. They ask us to create dozens of unique secrets, remember all of them, update them after breaches, spot phishing attacks, and avoid reusing them under pressure. That is a lot to expect from people who also forget why they walked into the kitchen.
Passkeys try to remove the most failure-prone part of authentication: human memory used under stress. That does not mean passwords will vanish tomorrow. They are still everywhere, and they remain deeply embedded in consumer and business systems. But the direction is clear. Big technology platforms are increasingly nudging users toward passwordless sign-ins because the current model depends too much on flawless behavior from imperfect humans.
Until that transition is complete, though, strong passwords still matter. In fact, they matter even more during the in-between stage. A weak password is like leaving your bike unlocked in a neighborhood where everyone has bolt cutters and bad intentions.
The Workplace Lesson Hidden Inside Consumer Password Data
One of the most useful things about U.S. password studies is that they expose how consumer behavior spills into workplace risk. People do not maintain two completely different security personalities. The same person who uses “Sunshine123” for a shopping account may be tempted to create “Welcome1” for a business tool if the system allows it.
That is why organizations need to design for realistic behavior instead of ideal behavior. Good password policy should not rely on wishful thinking. It should encourage long passphrases, block common and compromised passwords, support password managers, reduce unnecessary password rotation, and require multi-factor authentication. In other words, the goal is not to lecture humans into perfection. The goal is to build systems that protect humans from their own shortcuts.
When companies fail to do that, they are not just trusting employees. They are trusting every rushed Monday morning, every sleepy travel day, every reused password, every sticky note, and every “I’ll fix it later” decision that never gets fixed.
Conclusion: Predictable Choices Are the Real Password Problem
The latest U.S. password findings are not shocking because they reveal a brand-new threat. They are shocking because they confirm an old one that refuses to die. Americans still lean toward passwords that are easy to remember, easy to repeat, and easy to attack. The names and rankings may change, but the underlying behavior remains stubbornly familiar.
That makes the issue bigger than bad password taste. It is really a design problem, a behavior problem, and a scale problem all at once. People are overwhelmed by logins, drawn to convenience, and still trying to solve a modern security challenge with habits built for a much smaller internet.
The answer is not panic. It is better practice. Use longer passphrases. Use a password manager. Turn on MFA. Adopt passkeys when you can. Stop treating “slightly modified weak password” as a personality trait. Because in cybersecurity, predictable choices do not just look sloppy. They create openings.
Real-World Experiences That Explain the Data
To understand why password studies keep finding the same weak patterns, it helps to look at the everyday experiences behind them. Most bad password decisions are not made by reckless movie villains typing with evil laughter in the background. They are made by regular people in ordinary moments of minor stress. That is what makes the problem so persistent.
Picture a parent trying to sign up for a school portal, a grocery delivery app, a streaming service, and a telehealth account in the same week. Each site wants a password. Some require symbols. Some reject symbols. One wants eight characters. Another wants twelve. A third demands a capital letter, a number, and a blood oath. The result is rarely elegant. People fall back on whatever they can remember, and that often means some recycled favorite with a new number at the end.
Or think about the small-business owner setting up logins for a router, a payment dashboard, a printer console, a shipping tool, and a scheduling platform. Security is important in theory, but so is getting the store open by 9 a.m. That is how default passwords survive longer than they should, and how “admin” or “Welcome1” manages to keep popping up like a bad sequel nobody approved.
Then there is the breach moment, which is when password strategy suddenly becomes very real. It usually starts with an email that says your account information may have been exposed. You change one password. Then you realize you used a similar one on five other sites. Now you are spending your evening resetting accounts, checking your inbox for suspicious logins, and wondering why your 2021 shopping account is somehow holding your entire digital life hostage.
Another common experience is the household password economy. One person knows the Wi-Fi password. Another knows the streaming password. Somebody wrote the smart TV login on a scrap of paper. Someone else reused the same password for a retail site because “it is just for coupons.” Families and roommates build these little systems of convenience, and they work beautifully until one account gets compromised and everything starts unraveling in the least convenient order possible.
Even people who care about security get worn down. They mean to switch to a password manager. They mean to turn on MFA everywhere. They mean to stop reusing old favorites. But intentions lose to routine. And routine, more often than not, is where predictable passwords are born. That is why the data keeps looking familiar. It is not only measuring weakness. It is measuring human behavior under pressure, distraction, and digital overload.
Once you see it that way, the studies make perfect sense. Weak passwords are not just bad technical choices. They are coping mechanisms. The goal, then, is not to shame users for being human. It is to give them tools and habits that make the secure choice the easier choice. That is the only kind of password advice that has a fighting chance in real life.
Editorial note: This article synthesizes widely reported U.S.-relevant password research, cybersecurity guidance, and passwordless authentication developments from major security, government, and technology sources, with all source links intentionally omitted for publication cleanliness.